Securing Users, Apps, & Infrastructure Thru Zero Trust
The single biggest concern organizations face today is the security of their data, and the prevention of data exfiltration by a malicious actor—both externally and internally. It’s important to remember [...]
How to Plan a Safe Return for Your Hybrid Workforce
The Wall Street Journal called a hybrid workforce “a hacker’s dream,” and for a good reason. The size, number, and variety of devices passing into and out of an office, [...]
How to Rename Your Microsoft 365 Tenant
Since the dawn of time itself, there has been no ability to change the name of your Office and Microsoft 365 tenant. Once the tenant was created that was [...]
Improve Your Customer Experience with Contact Center AI
Today's AI-powered Contact Centers help create great experiences by solving customer challenges and simplifying purchases. Additionally, a Contact Center AI can provide your organization a more effective, efficient, and visible [...]
The State of Intelligent Automation (RPA) and the Digital Worker
Robotic Process Automation (RPA) has been around longer than you might realize. At its core, RPA simply means the automation of any, manually intensive IT or administrative task. For instance, [...]
4 Tools to Power Enterprise Mobility
The nature of work has changed. Never before has it been so critical that businesses be equipped for enterprise mobility. And with tools and technologies enabling employees to work [...]
4 Ways to Ensure Remote Work Security
As many companies move to permanent and hybrid remote work models, IT security has become even more of a top priority. As it becomes more common, it is crucial for [...]
Why Organizations Need DNS Threat Intelligence
The combination of a hostname and IP has been used to identify networked computers and services for decades. For most of that time, this has been a manual process, wherein [...]
Ransomware Maturation and Other Cybersecurity Threats
Here are the facts: Every week there's news of new breaches that impact global companies, major government institutions, and agencies. Unsurprisingly, ransomware attacks are on the rise with the United [...]
Why Use a Managed Service Provider? Top Questions Answered
Let’s talk about a Managed Service Provider, shall we? What does it entail, what might it include, and finally—how is it relevant to your business? A bevy of resources an [...]
5 Costly Mistakes to Avoid During Your Next Renewal Cycle
You’ve modernized your infrastructure, upgraded your storage and adopted new application, virtualization and security software. Now you can just sit back and let your new IT environment hum, right? Not [...]
Spring Boot Cold-Start Issues in AWS Lambda
Spring Boot has become the de facto standard for creating Microservices in Java. Since it’s widely used, Spring Boot has excellent community support. Traditionally, the Spring Boot application is used [...]
Automating Security at the Endpoint
Sophisticated cyberattacks which target the endpoint continue to be a major threat, and a significant risk. Ponemon reports that 68% of IT and security professionals said the frequency of cyberattacks [...]
Strategy & Factory Pattern in Spring Boot Application: Part II
Strategy and Factory patterns are the most useful design patterns in any application. If you have a branching code with lots of ‘if and else’, then Strategy pattern is the [...]
Strategy & Factory Patterns in Spring Boot Application: Part I
Strategy and Factory patterns are the most useful design patterns in any application. If you have a branching code with lots of ‘if and else’, then the Strategy pattern is [...]
5 Ways to Reduce Network Costs
As companies strive to control costs, networking teams must be ready to respond to calls for reductions. Unfortunately, network costs are traditionally considered tough to trim. After all, expensive single-manufacturer [...]
Migrating a VMware MS SQL Cluster with RDM Disks
When migrating your VMware environment to a new SAN or storage provider, edge cases often require special attention. One such case involves virtual machines with Raw Device Mapped (RDM) LUNs. [...]
Risk Assessment Can Protect Your Data and Business
Your business data is threatened by many types of risk – everything from natural disasters, data center outages, breaches by hackers, and even disgruntled employees. Mitigating the risk of data [...]
7 Key Tools for Network Security Teams Battling Cyber Threats
(and they don’t get in the way of business either) The elevated levels of cyber threat activity that now occur on a daily basis are leading most network security teams [...]
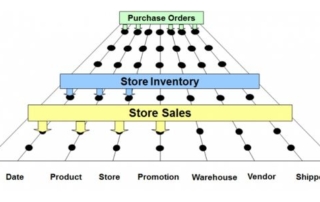
The Power of the Bus Matrix
When starting a data warehouse or business Intelligence effort, we go through a step-by-step process to get the information necessary to design and construct the pieces to satisfy the effort. [...]