The Current Situation
It’s perhaps a little misleading to go with the word current because the situation has been evolving for a little while, but it’s the most suitable word to use in a large number of cases that we encounter. However, the switchover to use a better system of delegating administration rights is gathering steam in the Microsoft partner community.
When a customer organization works with a Microsoft Partner or Cloud Services Provider, hereinafter just referred to as a CSP, a digital relationship is established using the Microsoft Partner Center Portal and the customer organization’s Microsoft 365 tenant.
The CSP creates an invitation and pastes it into an email for the customer organization to click on the links and accept the partnership. An example is shown below.
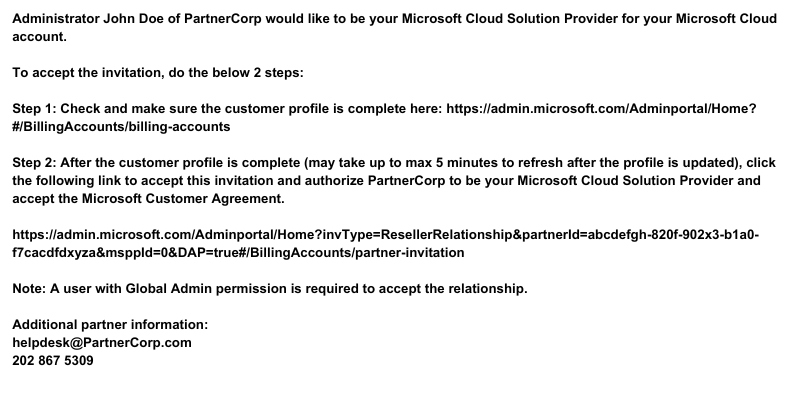
Note that there is a section we have highlighted in red. The current default in Partner Center is to select Delegated Admin Permissions. If customer organizations see the “DAP=TRUE” then that should not be accepted or even clicked on in fact, and the CSP requested instead to request a “Granular Delegated Administrative Privileges (GDAP) relationship.
Customer organizations can read more about DAP here, and GDAP here.
As can be seen from the frequently asked questions links above, DAP may still be necessary for the CSP to carry out certain functions. If the CSP is doing user support, processing support tickets, and managing licensing then there’s a case to be made for leaving the status quo in place assuming that there is a good activity monitoring and audit process in place.
How to GDAP
Setting up GDAP is significantly more work for the customer organization than DAP was and is. The first part is for the CSP to create the GDAP Relationship Request. For information, the process the CSP will follow is documented here. The CSP will click all the roles that have been agreed upon and send the customer organization the link to complete the first part of the process. These roles will have been worked out in advance of the CSP generating the request via conference call or email. It is a good idea to have the customer join a Teams call and for the Partner Portal screen to be shared to agree on the roles in real-time.
Once the agreement has been put in place the next phase will be carried out by the CSP. Simply having a GDAP relationship with the customer organization does not grant anyone at the partner access to anything in the customer organization tenant. The partner will now go through a process as outlined here. The CSP’s own tenant is where the security groups are created and where memberships are assigned. The Partner Portal is linked to the CSP’s tenant, and the security group is assigned to the Administration Relationship. Thus, only those support operatives that the CSP wishes to grant access may administer resources in the customer organization’s tenant.
Monitoring Access
With DEP, accounts for CSP support personnel to manage a customer organization’s tenant are created in the tenant and are just normal, albeit administrative, accounts and are therefore logged in the Activity Monitor in the normal way, but what of GDAP access?
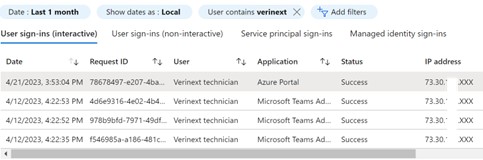
As with any other access, the logons of partner support personnel are still logged and tracked. This provides admins in the tenant information on the partner that accessed the service and whether Multi-Factor Authentication was applied, as shown in the image below, taken from the customer organization’s tenant sign-in logs.
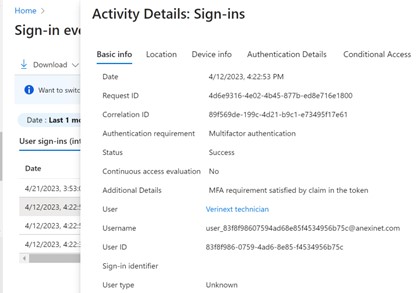
Unlike access from user accounts within the tenant where the full IP address is shown, only the first three octets are shown for GDAP access, notwithstanding the masking of the third octet in the example image below. I’ve masked the third octet merely as an additional nod to privacy.
Support Access
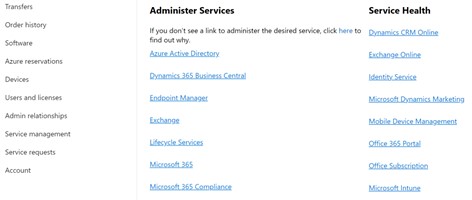
With DEP the support engineers log onto the customer organizations tenant directly but with GDAP access that is not the case. Engineers will use the Partner Portal to access the customer and select “Service Management” and then choose the service to administer. All services will be exposed but access will be granted only to the service to which the engineer has been assigned. Clicking the link to the service will open the customer tenant but with the partner engineer’s credentials. The “Service Health” column to the right is there to provide general information about Microsoft 365 services that may be experiencing issues.
Summary
Customer organizations can more closely control what their CSPs are permitted to do rather than grant a blanket global admin role to external support personnel. Implementing GDAP also permits a time period to be put onto any particular administrative request so that support projects can be permitted to expire and not leave hanging administrative privileges to remain, exposing the organization. It’s a little extra work for the customer and for the CSP but it’s worth it in terms of control, auditing, and accountability for all.
Learn more on how Verinext can assist you in your migration or contact us today.






